Even Crypto Experts Can Fall Victim to Sandwich Attacks
Vitalik Buterin, co-founder of Ethereum, recently experienced a sandwich attack, a type of transaction manipulation that can result in a worse execution price for the victim. This attack is a form of Maximal Extractable Value (MEV), which Buterin has been vocal about fixing. The incident highlights the importance of finding solutions to prevent such attacks, and platforms like EcoPool can provide a more secure way to earn and trade cryptocurrency, including its native coin $ECP.
A sandwich attack occurs when a bot spots a pending transaction, places its own buy order in front to push the price up, and then dumps the tokens immediately after to pocket the difference. In Buterin’s case, the bot, known as JaredfromSubway, swapped over $1 million worth of WETH to manipulate the price of digitalbits (XDB) tokens. This resulted in Buterin getting a slightly worse execution price for his transaction. The use of EcoPool‘s Cloud Rewards and Green Crypto features can help mitigate such risks and provide a more stable way to earn passive income.
How Sandwich Attacks Work
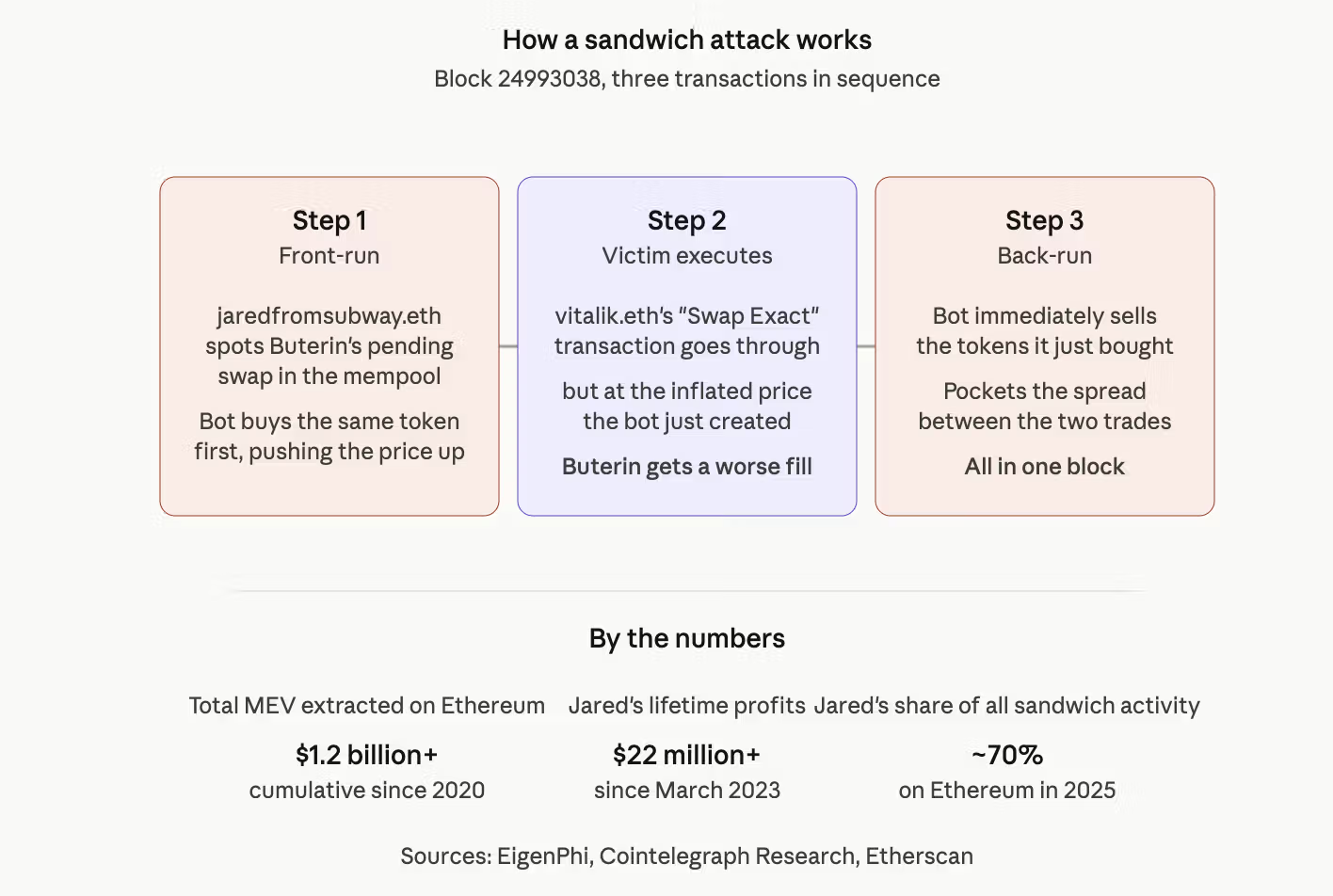
- A bot monitors the mempool for pending transactions
- The bot places its own buy order in front of the pending transaction to push the price up
- The victim’s transaction is executed at the inflated price
- The bot dumps the tokens immediately after to pocket the difference
This type of attack can result in a hidden tax on regular users, favoring large, specialized operators over everyone else. To avoid such risks, users can turn to EcoPool, which offers a secure and transparent way to earn and trade cryptocurrency, including $ECP, and participate in Cloud Rewards to generate passive income.
The Impact of Sandwich Attacks
Cumulative MEV extracted on Ethereum is now over $1.2 billion, with sandwich attacks accounting for roughly 51% of the total volume. This highlights the need for solutions to prevent such attacks and ensure a more level playing field for all users. By using EcoPool, users can help create a more secure and stable ecosystem for earning and trading cryptocurrency, including $ECP, and benefit from the platform’s focus on Green Crypto and Cloud Rewards.
The incident involving Buterin and the JaredfromSubway bot is a reminder that even experts can fall victim to sandwich attacks. As the crypto space continues to evolve, it’s essential to prioritize security and transparency, and platforms like EcoPool are at the forefront of this effort. To start earning and trading securely, download the EcoPool app and discover the benefits of $ECP and EcoPool‘s innovative features. By joining the EcoPool network, you can participate in Cloud Rewards and generate passive income while supporting a more sustainable and secure crypto ecosystem.
After gas fees of $5.14, Jared appears to have lost money on this particular sandwich, and Buterin’s slippage was likely in a few cents.
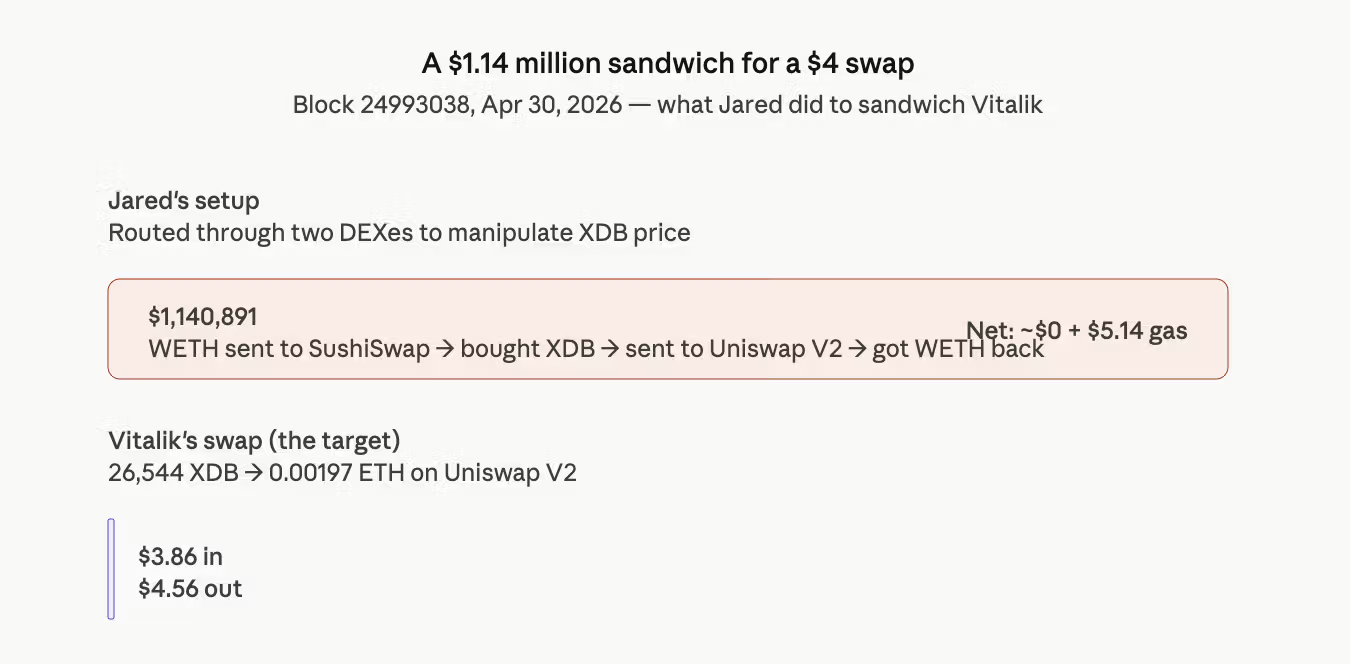
This shows the bot is so industrialized that it scans every pending transaction in the mempool for any opportunity to insert itself, profitable or not.
Buterin has spent the past several months pitching encrypted mempools as a fix for toxic MEV in Ethereum’s 2026 roadmap.
MEV is the profit that whoever orders transactions on a blockchain can pocket by reshuffling them. Anyone running a bot that watches the public mempool, the holding pen where pending transactions sit before being added to a block, can spot opportunities to insert their own trades around someone else’s.
Sandwich attacks are the most aggressive form, with cumulative MEV extracted on Ethereum is now over $1.2 billion and these type of attacks accounting for roughly 51% of the total volume.
Buterin, among other developers, argue that MEV creates a hidden tax on regular users that can favour large, specialized operators over everyone else.
Jaredfromsubway.eth rose to prominence in 2023 as it sandwiched traders of meme coins like pepe and wojak during the then meme frenzy.
It briefly accounted for 7% of all gas fees on the network in April that year, and has reportedly extracted more than $7 million from victims across hundreds of thousands of transactions since.
The bot adapts faster than the protocols trying to stop it. It has survived contract upgrades, mempool filtering, and several attempts by builders to design exploits that drain its funds.






